Research Article
Improving QoS of ad-hoc Networks by using SNR and T-AODV Routing Protocol
SCSVMV University, Kanchipuram, India
S. Rajalakshmi
SCSVMV University, Kanchipuram, India
Mobile ad-hoc Networks (MANET) plays a vital role in the critical applications such as military application, disaster recovery, etc. Collections of self-configured mobile nodes create the MANET network architecture. Each and every mobile node in the MANET is an autonomous node as MANET is a decentralized network. Since, all the nodes are mobile nodes, the topology of the network changes dynamically. So, the possibility of route failure is higher in the MANET than other static networks. The performance of the MANET should be increased as the emerging use of MANET in various applications. The performance of the MANET has affected by route failure, routing and communication overhead, lack of QoS and the signal fading.
Researchers mainly concentrate on path discovery to increase the performance of the MANET. ad-hoc On demand Distance Vector Routing protocol (AODV) is widely used for the route discovery in the MANET. The AODV routing protocol comes under the category of reactive routing protocol which means that it discover the route after receiving the Route Request (RREQ) from the source node. AODV handles the failure in the route discovered by sending the Route Error (RERR) message to the source node. Then the AODV reroute the data packets to the destination. The research is going on to improve the performance of AODV routing protocol in terms of security, energy efficiency, QoS parameters.
The enhancement of AODV protocol in the context of wireless ad-hoc network is proposed by Sharma et al. (2012). Weight hop based scheduling for AODV routing protocol is proposed in that study. In this technique, the relay node schedules the packet and manages its buffer memory depending upon the data transfer rate. If the failure occurs in the route, the relay node stores the data packet and repairs the route then reroute the data packet instead dropping the data. It mainly concentrates on the reliability of data transmission but it failed to consider the SNR value of the link before route the data packets.
AODV is most widely used for the ad-hoc networks because it achieves low routing overhead and high performance. A novel stable enhancement for AODV routing protocol is proposed by Zhong et al. (2003). This enhancement considers the stability of the node, load balance and the least remaining distance to select the path to the destination. When compared to AODV, it gives better performance. But it did not consider the strength of the signal received at the destination while travel through the route.
Metric based enhancement to AODV is proposed by Thanthry et al. (2006) to reduce the route failure. For that they consider the stability of the route while choosing the best path to reach the destination. EM-AODV routing protocol maintains multiple routes to the destination to share the traffic load. This protocol gives better performance when compared with AODV. But it fails to take the signal quality and the trustableness in to account.
Token routing Protocol is proposed by Cao and Lu (2010) for providing security in the energy efficient manner in AODV. It uses the hash chain algorithm to generate the token which is attached at the end of each data packet. The token is used for the authentication purpose. It provides security in the energy efficient manner but the major disadvantage is it did not consider any of the QoS parameters while selecting the route to reach the destination.
Ayash et al. (2012) proposed the improved AODV routing protocol. By reducing the control message overhead the performance of the AODV is enhanced. The new routing methodology called as AD-AODV is described by Wang et al. (2012), the hop count and the mobility of the node in the route is also take into consideration while selecting the best path to reach the destination. AD-AODV is mainly built to provide the best route in the highly dynamic environment. It does not consider the received signal strength and the authentication while routing the data.
The existing QoS routing scheme did not consider the strength of the signal and the trust ability of the mobile nodes into account. So, in this study, the novel metric such as SNR value and the trust value for route discovery phase of AODV is considered. The route to reach the destination has chosen first based on the distance, available bandwidth of the link and the stability of the mobile node in the route. The link which is having the highest SNR value is scheduled to take part in the route. Before that, the trust value is calculated for each and every node by collecting the information from the neighbor nodes. The trust value considers the parameters like honesty, energy, intimacy and QoS. As the node with highest trust value is scheduled as a relay node in the route, the QoS also get improved automatically. The following sections describe clearly about the newly proposed routing scheme in AODV (SNR and T-AODV).
Path selection takes an important part to improve the performance of ad-hoc network. The ultimate goal of network is effective communication. The communication includes reliable data transmission, secure data transmission, optimal data transmission. For some critical application like forest fire detection system the sensed data should be transmitted within a specific time period. It should reach the destination without time delay. In the wireless medium the data are transmitted in the form of signals. While the signals are transmitted through the air medium or free space, the signals are affected by fading and noise etc. In the study, no routing protocols consider the strength of the received signal while transmitting through the selected path. So, in this study, try to enhance the performance of AODV by considering the novel parameters signal to noise ratio and the trust value while choosing the path.
Addition of trust metric into the route discovery of AODV increases the QoS of the whole ad-hoc network. Trust value is calculated by considering the parameters like integrity, relationship, energy, QoS. The integrity and degree of relationship between the nodes in the ad-hoc network provides the authentication between the nodes to enhance the security. The nodes which are having highest trust worthiness are going to be participating in the route to reach the destination.
Figure 1 explains the concept of the proposed methodology. The trust value is estimated for each and every node in the ad-hoc network. Trust value is estimated by collecting the previous history information from the neighbor nodes. By transmitting the test signals, the signal to noise ratio is also calculated for each and every link between the nodes. These two additional parameters are given as input to the route discovery phase of AODV. The AODV discover the route only on demand.
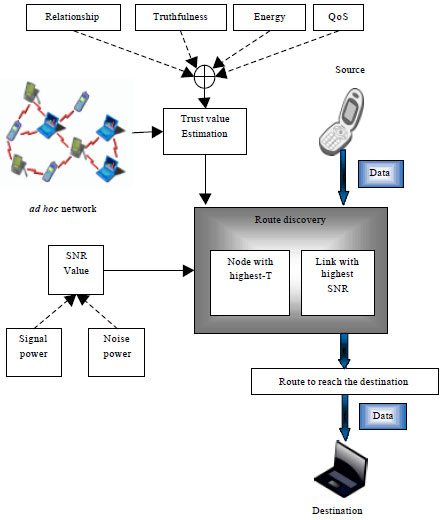 | |
| Fig. 1: | Block diagram of SNR and T-AODV routing scheme |
The nodes which are having highest trust value and the link with highest SNR value are scheduled as a route to reach the destination. As the SNR value is also consider as a routing discovery parameter, the strength of the received signal is more or less equal to the strength of the signal at the sender side.
Estimation of trust value: The trust value estimation process is clearly explained in Fig. 1. The trust value is easy to calculate. Equation which is used for the calculation of trust value is given below:
![]()
The Trust value is the addition of the node’s truthfulness to its neighbor nodes, Node’s relationship with its neighbor nodes, energy of the node and the QoS achieved by that particular node.
NTruthfulness: It indicates the belief of node N’s neighbors. The node N is honest depending upon the entire neighbor node’s direct examination towards node N for a particular time period t. Each and every node maintains the count of dishonest behavior of its neighbors. That is estimated by set of malicious node detection rules as by Da Silva et al. (2005). If the count value is higher than the system threshold value that node is considered as totally untruthful at time t that is the value of NTruthfulness = 0. Otherwise it is computed by subtracting the ratio of the count value from 1.
NRelationship: It says the how the particular node is interact with each other. It is computed by taking the count of number of interaction between its neighbor nodes over the maximum number of interaction between node N and any one of its neighbor node within the time period t.
NEnergy: This value is estimated to evaluate whether a particular node has adequate energy to perform its function. It is computed by the amount of node N’s residual energy by using the energy consumption model by Budianu et al. (2006).
NQoS: The Quality of service parameter is the important parameter. In this study, following parameters only taking into account to calculate the QoS value: Packet Delivery Ratio (PDR), Packet Loss Ratio (PLR), delay time. The PDR of node N refers to the number of packets delivered to all of its neighbors per unit time t. PLR indicates that the ratio of packet loss during time t. Delay means that the time between the current packet receiving and the last packet received.
The signal to noise ratio is computed for the entire link exists between the nodes by transmitting the test signal dynamically. The SNR value of node N is computed in accordance with all of its neighbors. Generally in wireless communication the node having the link with all the nodes within its communication range. The following equation is used to calculate the SNR value:
![]()
Where:
| NSNR | = | Signal to noise ratio of node N |
| Rx_Thresh | = | Receiving threshold value |
| Noise_P | = | Signal noise power |
The source node indent to find the route to reach the destination means the source has to transmit Route Request (RREQ) packets. In the proposed routing scheme, the source node sends the RREQ packet to any one of its neighbor. The source node selects the forwarder node by analyzing all of its connected nodes. Then, it chooses the node with highest trust value and the max SNR value in the link between the source and its neighbor node. The RREQ passes in this way until it reach the destination or the node which is having the route to reach the destination. As AODV consider these parameters while choosing the route, the QoS is improved and the security level is also enhanced. The evaluation of proposed scheme is done by using NS2 simulator and the results are presented below.
The performance is evaluated by comparing the results obtained by proposed scheme (SNR and T-AODV) with existing QoS related routing protocol (Q-AODV). The proposed method includes the Qos parameter as well as mainly considers the SNR and Trust value. So, the results show that, the proposed method work well than existing Q-AODV. Proposed SNR and T-AODV is evaluated by considering 30 numbers of nodes. As the network is the ad-hoc network, random way mobility model is used for describing the movement of all the nodes in the simulation area of 1000x1000. The performance of the proposed scheme is evaluated by packet delivery ratio, packet loss ratio, delay and the received signal strength. The parameters to configure the nodes in the ad-hoc networks are shown in the following table.
The parameters present in Table 1 is used to configure all the mobile nodes participate in the simulation. By analyzing the entry in the Table 1, 30 number of nodes move within the area 1000x1000 by using random way mobility model. The UDP protocol is used to make the communication link between the sender and the receiver. The traffic mode CBR is used to handle the traffic flow in the network. The propagation model is used to sanctify the way radio waves are propagated from one place to another. The omni antenna is used to receive the signals from all direction. Each node participate in the simulation is configured with the parameters mentioned in Table 1.
The RSS indicates that the strength of the signal received at one particular node. It is calculated by using the gain of transmitting and receiving antenna. In simulation the gain of both the antenna is assumed that 1 dB. Received signal strength varies according to the distance. Figure 2 shows that the strength of the received signal at destination node. It shows that the received signal strength at the destination side is high when compared with Q-AODV protocol.
The delay during the data transmission is recorded in the trace file when using Q-AODV and SNR and T-AODV. Figure 3 shows that the delay has been very low when compared with Q-AODV protocol because of the consideration of trust value. As the source node transmits data packet only via., trusted node, the delay is reduced.
| Table 1: | Simulation parameters of SNR and T-AODV |
 | |
 | |
| Fig. 2: | Analyses of RSS of proposed SNR and T-AODV and comparison with Q-AODV routing protocol |
 | |
| Fig. 3: | End to end delay occur in the network while using SNR_T AODV and Q-AODV |
Figure 4a shows the analyses of packet delivery ratio of proposed SNR and T-AODV and comparison with Q-AODV routing protocol.
Packet delivery ratio indicates that the number of packets delivered to the destination for the unit time period. Figure 4a clearly says that, the proposed technique achieves high PDR when compared with Q-AODV. The packet delivery ratio is also one of the QoS parameter. So, the higher value of packet loss rate indicates the better performance of the proposed method.
 | |
| Fig. 4(a-b): | (a) Analyses of packet delivery ratio of proposed SNR and T-AODV and comparison with Q-AODV routing protocol and (b) Analyses of packet loss ratio of proposed SNR and T-AODV and comparison with Q-AODV routing protocol |
The number of packets dropped during the simulation time is recorded and while executing the recorded trace file the graph which is shown in Fig. 4b received. The packet drooping occurs due to some malicious node present in the network. Since, the trust value is considered as the routing parameter, the packet loss is low when compared with Q-AODV.
In this study, SNR and T-AODV protocol is proposed. It means that the signal to noise ratio and the trust value is also included to discover the route between source and the destination. The consideration of trust value as the path selection parameter, the security level is increased and the QoS is also enhanced. The consideration of SNR value increase the strength of the received signal as the data packets are transmitted via the nodes with highest SNR value. The simulation results shows that the proposed technique provides high performance in terms of PDR, PLR, delay and the received signal strength.