Research Article
Random Image Steganography using Pixel Indicator to Enhance Hiding Capacity
Saranathan College of Engineering, Trichirapalli, Tamil Nadu, India
Y. Venkataramani
Saranathan College of Engineering, Trichirapalli, Tamil Nadu, India
Cryptography can be explained as the transformation of meaningful information into a scrambled code using a key (or keys). The receiver can decode with the help of a key to revive the plaintext. The fundamental notion of cryptography is that between one to one communications (Schneier, 2007; Zaidan et al., 2010), impostor should not or cannot extract the covert data. Depending on the complexity required same keys or different keys can be used for both encryption and decryption. The broad classifications of cryptography are private key cryptography and public key cryptography. For a good cryptographic algorithm, emphasis is laid on key length, type of key (duration of key like session key), lifetime of keys, complexity and security of the algorithm, encrypting procedure (double or triple encryption), medium of transmission and so on.
Steganography (Bender et al., 1996, 2000) crams the plan of veiling secrets in innocuous media keen on the communication between two parties so that, a third party cannot sense the secret’s subsistence (Amirtharajan et al., 2011, 2012, 2013a-g; Cheddad et al., 2010; Hmood et al., 2010a, b; Janakiraman et al., 2012a, b; Mohammad et al., 2011; Padmaa et al., 2011; Praveenkumar et al., 2012a, b, 2013a, b; Rajagopalan et al., 2012; Stefan and Fabin, 2000; Thenmozhi et al., 2012; Zanganeh and Ibrahim, 2011). The universal theory underlying a large amount of steganographic methods is to situate the covert data in the message’s noise component. If the information is coded such that it is impossible to differentiate from true noise, a intruder cannot perceive the secret message. To withstand security attacks, any steganographic algorithm should be robust, safe and sound (Chan and Cheng, 2004; Gutub, 2010; Hong et al., 2009; Luo et al., 2008, 2011; Zanganeh and Ibrahim, 2011; Zhao and Luo, 2012; Zhu et al., 2011).
A secures steganographic algorithm should satisfy 4 prerequisites, viz., there should be a unique secret key to every sender; the holder of the truthful key only can detect and access the concealed message; though the attacker recognizes a part of the hidden content, he or she should not be able to detect the remaining; it must be computationally difficult to detect secret messages. While spatial domain schemes (Al-Azawi and Fadhil, 2010; Amirtharajan and Rayappan, 2012a-d, 2013; Thanikaiselvan et al., 2011; Thanikaiselvan et al., 2012a, b, 2013; Xiang et al., 2011; Yang et al., 2011; Zaidan et al., 2010) exploits LSB, PVD (Padmaa et al., 2011), Pixel Indicator methods PIs (Gutub, 2010; Padmaa et al., 2011; Amirtharajan et al., 2011, 2012, 2013d), transform domain involves DCT, DFT, DHT, DWT. Steganography is useful in ownership verification, electronic labeling, copyright protection, piracy and many more and the counter attack is steganalysis (Qin et al., 2009; 2010; Xia et al., 2009).
Digital Watermarking refers to the techniques which are used to hide confidential information in digital media (Zeki et al., 2011). Robust portrays the capacity of the watermark to survive manipulations of the file, such as lossy compression, cropping, scaling just to spell out some. Fragile means the watermark must not oppose tampering, or would do so only upto a certain extent. At present, watermarking concept is widely employed in e-commerce, tamper detection, advertising, broadcasting, customized media delivery, fraud detection and many more. Needless to mention the threats posed to this scheme. Some of them are collusion attacks, transcoding, linear and nonlinear filtering, signal enhancement. Since online communication in each and every way has seen a phenomenal evolution, watermarking has become the field of interest and numerous procedures are discovered to combat the above mentioned problems.
This study proposed a method to improve the imperceptibility of the random image steganography without compromising the payload. The next section describes the materials and methods with the algorithm and flowchart of the proposed method. The followed section gives the results with comparison then the final conclusion of this study.
In Steganography, seemingly random changes are introduced to the cover image, based on the secret data. The algorithms construct a robust security for the secret, at the same time without impacting the embedding capacity and imperceptibility (Amirtharajan and Rayappan, 2012a-d).
There exist varieties of algorithms that make use of LSB substitution and Pixel Indicator techniques for hiding data, But the routine used to build this method of steganography distinguishes itself from the others in the manner that, a high quality stego image is created by using more features of the cover images. Unlike conventional LSB substitution, pixel value decides embedding. Pixel indicator concept is employed for the selection of plane for embedding. The embedding process starts from the leftmost pixel and moving downwards (i.e., column wise scanning is adapted to increase the security).
Moreover, a match between the secret bits with that of the original is searched. For k = 4 bit embedding, if a match is found secret data is not embedded and if it is not so, pixel bits experience embedding. The starting bits of the matches are combined to form a bit stream which is nothing but the stego key. The receiver should be let known of this key for the recovery process. Here three such methods are suggested.
Method 1: It takes the default indicator as red channel, green and blue are say, data channels. If the value of the indicator is:
| 00: | Data is not embedded |
| 01: | Data is embedded in blue plane |
| 10: | Data is embedded in green plane |
| 11: | Data is embedded in both planes |
Data embedding, here, obeys the rules of defined LSB substitution in the corresponding planes.
Method 2: This method is slightly different from method 1. Here user is allowed to set the indicator channel and the remaining two act as data channels.
If the value of the indicator is:
| 00: | Data is not embedded |
| 01: | Data is embedded in 1st plane |
| 10: | Data is embedded in 2nd plane |
| 11: | Data is embedded in both planes |
Data embedding, here, obeys the rules of defined LSB substitution in the corresponding planes.
Method 3: Cyclic indicator routine is followed here. All planes are named indicator cyclically. That is if red is made the indicator for first pixel (green and blue act as data channels), green is made the indicator for the second pixel (red and blue act as data channels), blue for the third (green and red act as data channels), again red for fourth and so on and is shown in Fig. 1.
EMBEDDING ALGORITHM
The proposed method Flow chart for embedding is shown in Fig. 2.
Method 1: |
 |
 | |
| Fig. 1: | Block diagram for proposed method |
 | |
| Fig. 2: | Flow chart for embedding |
Method 2: |
 |
Method 3: |
 |
EXTRACTION ALGORITHM
The proposed method Flow chart for extraction is shown in Fig. 3.
 | |
| Fig. 3: | Flow chart for extraction |
 |
Four color cover images of dimension 256x256 each are taken to verify the performance of the algorithm. These images go through the testing of full embedding capability for all three methods. To have a vision about the efficacy, corresponding stego images are generated and studied (Fig. 4-7). MSE and PSNR values are calculated, Table 1-3 and compared. The mathematical equations for doing so are:
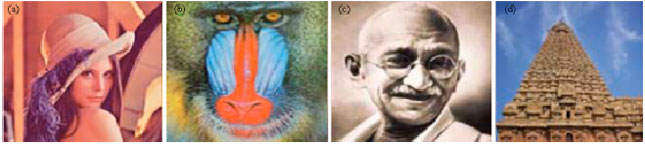 | |
| Fig. 4(a-d): | Stego and cover images (a) Lena, (b) Baboon, (c) Mahatma Gandhi and (d) Temple |
| Table 1: | MSE, PSNR values for method 1 |
 | |
| Table 2: | MSE, PSNR values for method 2 |
 | |
| Table 3: | Comparison with existing methods for MSE, PSNR and BPP values for method 3 |
 | |
If PSNR is high, stego image is highly imperceptible that is it suffers from negligible distortion. For four bit embedding, the probability that a 4-bit match is found in the bit stream will be 1/16. For example, if search is for 1011, it may be in the range from 0000 up to 1111. The chance for finding a match increases with the increase in bits used for searching in pixels in the cover.
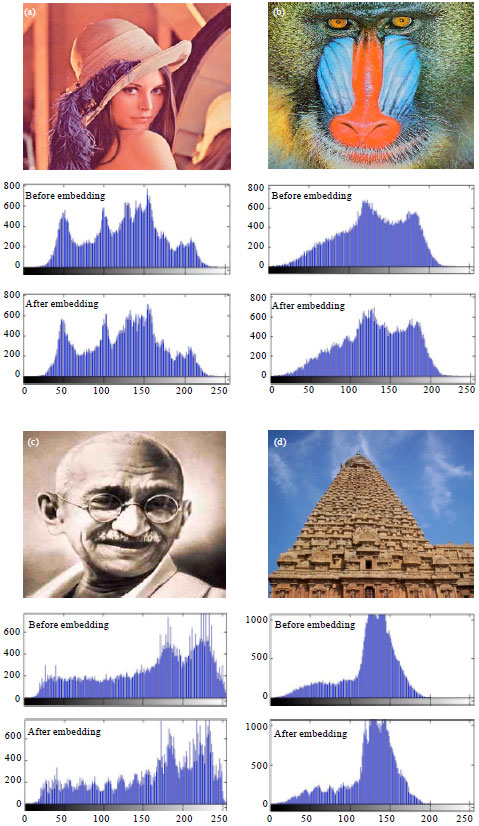 | |
| Fig. 5(a-d): | Resultant stego images and their corresponding Histograms for Method 1. Cover images (a) Lena, (b) Baboon, (c) Mahatma Gandhi and (d) Temple |
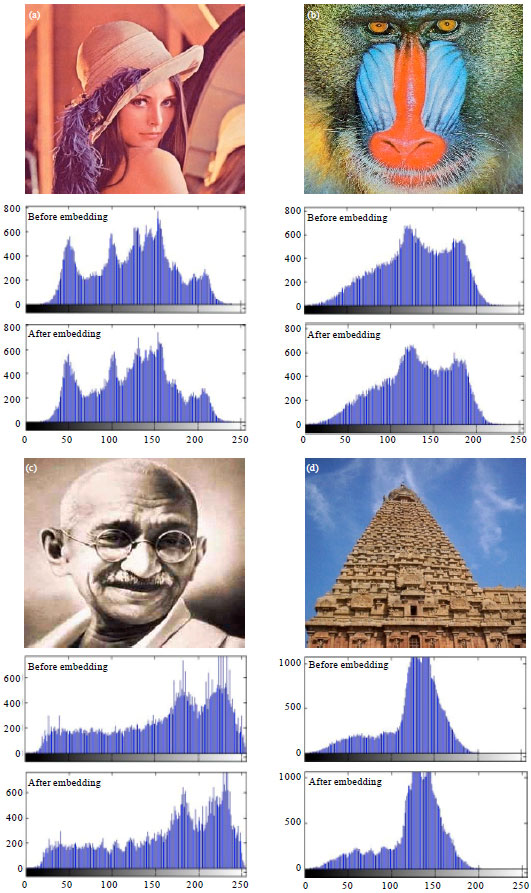 | |
| Fig. 6(a-d): | Resultant stego images and their corresponding Histograms for Method 2. Cover images (a) Lena (b) Baboon (c) Mahatma Gandhi and (d) Temple |
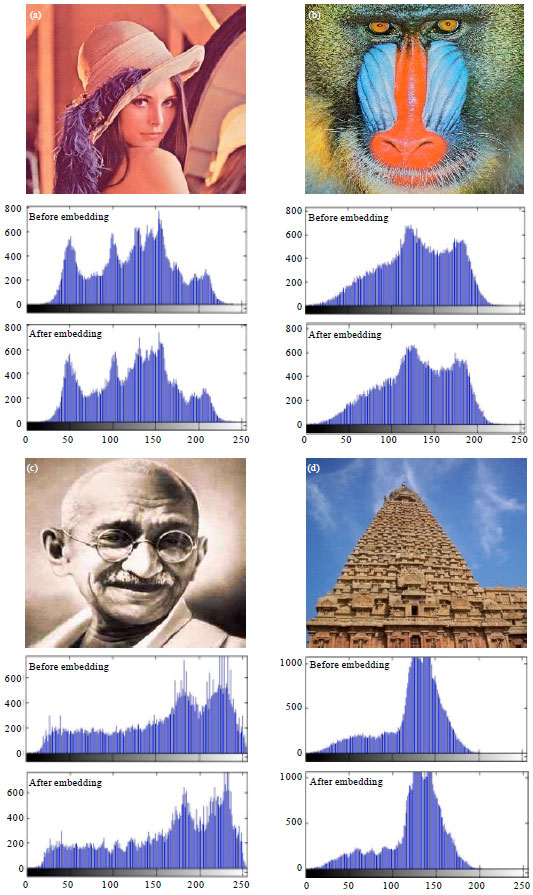 | |
| Fig. 7(a-d): | Resultant stego images and their corresponding Histograms for Method 3. Cover images (a) Lena, (b) Baboon, (c) Mahatma Gandhi and (d) Temple |
If there does not exist a match, then the secret 4 bits are set in first four LSBs.
From the stego images we can infer that it is completely free of distortion and escapes human suspicion. Higher PSNR values of stego images guarantees that they are of fairly high quality.
An inimitable approach is presented in this script to settle the significant problem of capacity of payload and imperceptibility in a steganographic scheme. This study makes use of Pixel Indicator and modified Least Significant Bit Substitution methods to construct the algorithm and also OPAP to reduce the distortion. Also the key used for encryption and stego key are not identifiable as the latter is based on the position of the bits of the original cover. The algorithm’s strength is it could withstand steganalysis attack with the help of four color images. This method involves some computational forehead which indeed resists itself to security threats. The images do not suffer from artifacts as only the LSBs of the pixels undergo alteration. Thus, this study provides security both at the steganographic and cryptographic level. Tentative results also affirm the conclusion. Thus, it is an effective way of secret data communication.
The first author wishes to thank Dr. R. Amirtharajan Associate Professor/ECE School of Electrical and Electronics Engineering, for his valuable guidance to improve technical and linguistic quality of this study.