ABSTRACT
Many previous visible image watermarking schemes are not applicable for document images. A novel visible watermarking algorithm is proposed by considering the unique visual perception of document images. To obtain good visual quality of watermarked images and good perceptual watermark translucence, an adaptive scaling factor and embedding factor calculation method is designed by exploiting luminance and edge masking characteristics of document images. Experimental results prove that the scheme has both good visual quality of watermarked images and satisfactory visible watermark translucence. In addition, it successfully resists removal attacks.
PDF Abstract XML References Citation
How to cite this article
DOI: 10.3923/itj.2012.1322.1326
URL: https://scialert.net/abstract/?doi=itj.2012.1322.1326
INTRODUCTION
Digital image visible watermarking is a type of digital watermarking technology (Phadikar et al., 2007; Shirali-Shahreza and Shirali-Shahreza, 2008; Islam et al., 2008; Prasannakumari, 2009; Abdulfetah et al., 2009) used for protection of publicly available images. It offers a wide range of potential applications in many fields such as digital libraries, digital TV, e-commerce and video on demand via the internet. Different from invisible watermarking algorithms (Liang et al., 2011; Olanrewaju et al., 2011; Shilbayeh and Alshamary, 2010; Zeki et al., 2011; Yang et al., 2010), the visible watermarking schemes embed watermarks into digital contents translucently by overlaying recognizable but unobtrusive copyright patterns (watermarks). The watermark should be noticeable yet must not significantly obscure the image details beneath it. A well-designed visible watermarking technique should retain all details of host contents. At the same time, the watermark must be difficult or even impossible to remove. Many visible watermarking approaches have been proposed in literature. Braudaway et al. (1996) presented an earlier visible watermarking approach in spatial domain to mark the digitized pages of manuscript from the Vatican archive. Mohanty and Ramakrishna (2000) designed a visible image watermarking in DCT domain by employing the texture sensitivity of the Human Visual System (HVS) and modifying the DCT coefficients of the host image. Hu and Kwong (2001) gave a scaling factors calculation strategy based on the effect of luminance and local spatial characteristics and implement a wavelet based visible watermarking technique. Biao-Bing and Tang (2006) proposed a visible watermarking algorithm in discrete wavelet transform domain by using a contrast-sensitive function. This approach provided good watermark visual effect on watermarked images. Min-Jen et al. (2011) presented an Adaptive visible image watermarking approach in wavelet transform domain by incorporating contrast sensitivity. The strength of the watermark within the wavelet decomposition sub-bands is adjusted according to this sensitivity. The proposed method has excellent robustness and transparency. Zeng and Wu (2010) described a spatial image adaptive visible watermarking scheme by considering both the host image and visible watermark features. However, all the above-mentioned schemes the unique characteristics of document images and they are not applicable for document images.
To protect copyright of digital document images in digital library, we propose an adaptive visible watermarking scheme for document images by exploiting the luminance and edge sensitivity of document images.
CALCULATION OF SCALING FACTOR AND EMBEDDING FACTOR
To obtain a well trade-off between the watermark embedding energy and the quality of perceptual watermark translucence during visible watermark embedding, it is important to exploit the visual perception host images.
Human visual perception is more sensitive to distortion in blocks with mid-intensity values than that of low intensity blocks as well as high intensity blocks. In fact, sensitivity drops parabolically as the gray value drifts on both sides. So, luminance masking used can be described by the formula:
| (1) |
where, θ(x, y) denotes luminance masking, I (x, y) is the gray value of a pixel with coordinates x and y,![]() is the mean gray value of the host image, μ'max is the maximum value of μ' (x, y).
is the mean gray value of the host image, μ'max is the maximum value of μ' (x, y).
The edge is an important image structure. Human eyes are very sensitive to the noise in image edge areas. Since, Image edge areas have greater variance value while smooth image areas have smaller variance value, the edge feature can be reflected by variance δ (x, y) (note that: the variance is calculated in an image neighbor with size 3x3). The edge visual factor (λ(x, y)) is defined by the normalized variance as:
| (2) |
where, δmax is the maximum value of δ (x,y).
Document images have a distinctive feature that they are composed of text areas and non-text areas (background). Text area is black or near black, but large background areas, usually white or near white. These areas can tolerate large gray value change. This means that the scaling factor a (x, y) will monotonically decrease with luminance masking θ (x, y) while the embedding factor β (x, y) monotonically increase. Moreover, the edge areas locate on the junctions of text and non-text areas in document images. Border region should avoid significant distortion during watermark embedding. For simplicity, we can assume the scaling factor a (x, y) to be directly proportional to the edge visual factor λ (x, y). The variation of the embedding factor β (x, y) with respect to the edge visual factor λ (x, y) is the reverse of that of the scaling factor a (x, y).
According to the above considering, a (x, y) and β (x, y) can be computed as follows:
| (3) |
Finally, to achieve a flexible and controllable visible watermark embedding, we normalize the scaling factor and the embedding factor to a closed interval [a, b] (where, 0<a<b<1) and obtain normalized a (x, y) and β (x, y) by the following formula:
 | (4) |
where, function max() and min() return the maximum and minimum value of an expression, respectively.
VISIBLE WATERMARK INSERTION FOR DOCUMENT IMAGE
In visible watermark embedding for document images, our scheme considered the unique characteristics of document images by exploiting the luminance and edge masking characteristics. The whole visible watermark embedding process is described as follows:
| Input: | Watermark image W, original document image I |
| Output: | Watermarked document image I' |
| Step 1: | Read the original document image I and the watermark image W |
| Step 2: | Compute the scaling factor a(x,y) and the embedding factor a(x,y) for each pixel according to Eq. 4 |
| Step 3: | Choose an image pixel of the original document image for visible watermark embedding |
| Step 4: | The corresponding watermark message bit W(x,y) is embedded by modifying pixel value I(x,y) of document image I as follows: |
| (5) |
| Step 5: | Repeat step 3-step 4 until all the watermark bits are embedded into the host document images and finally the watermarked image I' is generated |
EXPERIMENTAL RESULTS
In This study, some gray-scale document image with size 512x512 are adopted as test images and watermark images are grayscale images with recognizable pattern which have the same size as the host document images. Parameters a and b in Eq. 4 value 0.1, 0.9, respectively.
Figure 1 and 2 show the watermark image and four test document images.
 | |
| Fig. 1: | Watermark image |
 | |
| Fig. 2(a-d): | Test document images |
 | |
| Fig. 3(a-d): | Watermarked images generated by our scheme |
| Table 1: | Watermarked image visual quality (PSNR) comparison between the proposed method and Zeng and Wu (2010) (dB) |
Figure 3 shows the visible watermarking experimental results carried out on test document images shown in Fig. 2 and watermark image as seen in Fig. 1. In addition, we have also compared the proposed scheme with Zeng and Wu (2010) and the detailed comparison experimental results are listed in Table 1.
From Fig. 3, we know that the watermarked images have good visual quality and that the quality of perceptual watermark translucence is pleasant. PSNR comparison results in Table 1 illustrates that our approach obtains about 2 dB higher PSNR value of watermarked images than Zeng and Wu (2010) on average.
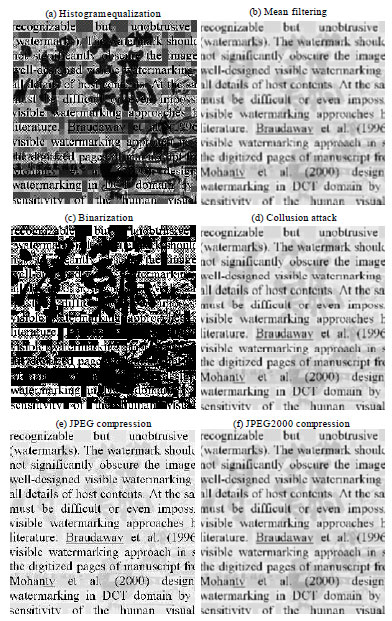 | |
| Fig. 4(a-f): | Robustness against removal attacks, the watermarked image (a-f) are obtained by histogram equalization, mean filtering with 3x3 window, image binarization with threshold 240, averaging 25 different watermarked image versions, JPEG compression with quality factor 10 and JPEG 2000 compression with compression ration 60:1, respectively |
The proposed scheme can get an optimal trade-off between the watermark embedding strength and the perceptual watermark translucence. This is because that our scheme considered the document image visual perception especially by combining luminance masking and edge masking characteristics.
In addition to watermarked imaged quality and perceptual watermark translucence, the visible watermark imposed on host document images must be difficult to remove. That is to say, visible watermarking schemes should be robust against common attack operations such as image compression, image enhancement, image filtering and collusion attack and so on. Take Fig. 2a as an example, the illustration of robust ness experimental results is shown in Fig. 4. We can see that the watermarked document images have satisfactory visible watermark translucence and that the proposed document image visible watermarking technique is robust against ordinary signal processing attacks.
CONCLUSIONS
An adaptive visible watermarking technique for document images has been proposed in spatial domain by exploiting the unique visual perception of document images. The scaling factor and the embedding factor are adaptive to document image content due to the combination of luminance masking and edge masking. The proposed scheme achieves best trade-off between the watermark strength and the perceptual watermark translucence and it obtains pleasant document image quality, watermark visibility and robustness to common removal attacks. It will have widely applications in digital media fields such as digital library, digital cinema and digital publishing.
ACKNOWLEDGMENTS
This study was supported by Youth Foundation of Research Program of Humanities and Social Sciences of Chinese Ministry of Education (10YJC870014), National Natural Science Foundation of China (61073191), Hunan Provincial Philosophy and Social Sciences Foundation of China (11YBA090), Hunan Provincial Natural Science Foundation of China (10JJ6090), Scientific Research Fund of Department of Science and Technology of Hunan Provincial, China (2011GK3140), Science and Technology Innovative Research Team in Higher Educational Institutions of Hunan Province (2010212).
REFERENCES
- Phadikar, A., B. Verma and S. Jain, 2007. Region splitting approach to robust color image watermarking scheme in wavelet domain. Asian J. Inform. Manage., 1: 27-42.
CrossRefDirect Link - Shirali-Shahreza, M. and S. Shirali-Shahreza, 2008. High capacity persian/arabic text steganography. J. Applied Sci., 8: 4173-4179.
CrossRefDirect Link - Islam, M.R., M.S. Sayeed and A. Samraj, 2008. A secured fingerprint authentication system. J. Applied Sci., 8: 2939-2948.
CrossRefDirect Link - Prasannakumari, V., 2009. A robust tamperproof watermarking for data integrity in relational databases. Res. J. Inform. Technol., 1: 115-121.
CrossRef - Abdulfetah, A., X. Sun and H. Yang, 2009. Quantization based robust image watermarking in DCT-SVD domain. Res. J. Inform. Technol., 1: 107-114.
CrossRefDirect Link - Liang, W., J. Xu and J. Long, 2011. A high-capacity lossless algorithm for watermarking binary images. Res. J. Inf. Technol., 3 : 229-236.
CrossRef - Olanrewaju R.F., O.O. Khalifa, A. Abdullah, A.A. Aburas and A.M. Zeki, 2011. Determining watermark embedding strength complex valued neural network. J. Applied Sci., 11: 2907-2915.
CrossRefDirect Link - Shilbayeh, N.F. and A. Alshamary, 2010. Digital watermarking system based on cascading haar wavelet transform and discrete wavelet transform. J. Applied Sci., 10: 2168-2186.
CrossRefDirect Link - Zeki, A.M., A.A. Manaf, A.A. Ibrahim and M. Zamani, 2011. A robust watermark embedding in smooth areas. Res. J. Inform. Technol., 3: 123-131.
CrossRef - Yang, H., X. Sun and G. Sun, 2010. A semi-fragile watermarking algorithm using adaptive least significant Bit substitution. Inform. Technol. J., 9: 20-26.
CrossRefDirect Link - Braudaway, G.W., K.A. Magerlein and F.C. Mintzer, 1996. Protecting publicly available images with a visible image watermark. Proceedings of the SPIE Conference on Optical Security and Counterfeit Deterrence Technique, February 1-2, 1996, San Jose, CA, USA., pp: 126-133.
CrossRef - Mohanty, S.P. and K.R. Ramakrishna, 2000. A DCT domain visible watermarking technique for images. Proceedings of the IEEE International Conference on Multimedia and Expo, July 30-August 2, 2000, New York City, USA., pp: 1029-1032.
Direct Link - Hu, Y.J. and S. Kwong, 2001. Wavelet domain adaptive visible watermarking. Electron. Lett., 37: 1219-1220.
CrossRefDirect Link - Biao-Bing, H. and S. Tang, 2006. A contrast-sensitive visible watermarking scheme. IEEE MultiMedia, 13: 60-66.
CrossRefDirect Link - Min-Jen, T., J. Liu and C. Chuang, 2011. The adaptive content and contrast-aware technique for visible watermarking. Proceedings of the 6th International Conference on Systems and Networks Communications (ICSNC 2011), October 23-29, 2011, Barcelona, Spain, pp: 38-42.
Direct Link - Zeng, W. and Y. Wu, 2010. A visible watermarking scheme in spatial domain using HVS model. Inform. Technol. J., 9: 1622-1628.
CrossRefDirect Link








