Research Article
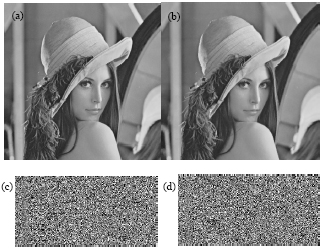
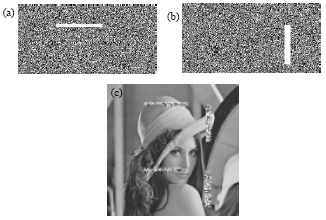
Joint Secret Sharing and Data Hiding for Block Truncation Coding Compressed Image Transmission
School of Aeronautics and Astronautics, Zhejiang University, Hangzhou 310027, China
Zhenfei Zhao
School of Information Science and Technology, Sun Yat-sen University, GuangZhou 510006, China
Zhe-Ming Lu
School of Aeronautics and Astronautics, Zhejiang University, Hangzhou 310027, China